In Business, only a few things are as important as maintaining the security of sensitive data. It’s no wonder then that today’s organisations, whether large or small, spend a lot of time and money in corporate security. With the advancement of technology, Network Security Management has become much more challenging than what it used to be even a few years ago. Now you need security checks at every entry point – starting from the desktop to the cloud server. In this context, it is essential for all business to follow some best practice guidelines for network security.
Network Security in London:
What about Hiring a Professional Service:
Professionals who have years of experience in managing VPN, WAN, LAN, VOIP networks would be able to monitor your network infrastructure on a daily basis, and thus eliminate or at least reduce the risks. Top IT support companies like WinMax IT provide stringent network security in London. They secure your hardware infrastructure and security software against any possible malicious attacks. They usually provide a wide range of services, which include configuring and managing firewalls, scanning for vulnerabilities, ensuring proper management of security patches and spontaneous intrusion detection, devising of techniques for protocol and packet filtering, and SSL and VPN security. It is always a good idea to select a vendor that constantly keeps track of technological advancements, and upgrades its security measures accordingly.
What are Some Best Practices to Follow?
Here are some steps that you can take for Network Security Management.
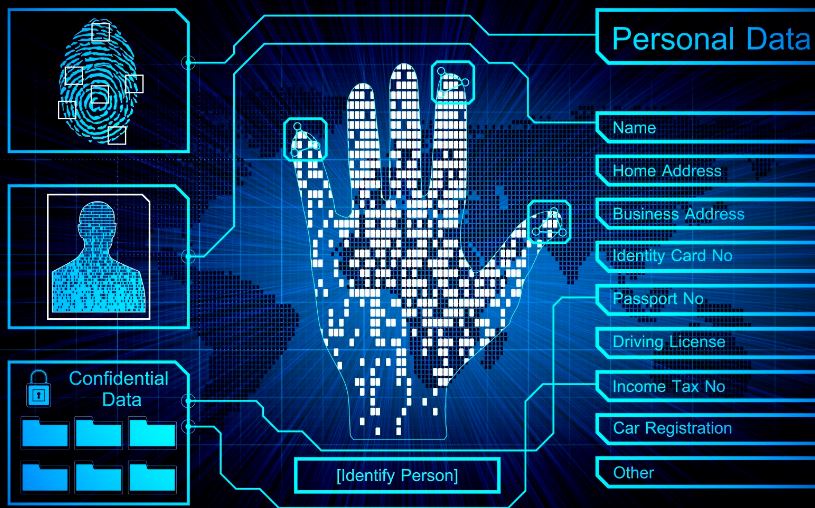
• Encrypt sensitive data
It is always safe to encrypt your critical data, so as to protect it against any kind of security threats. This also helps to prevent data loss in the event of theft or loss of equipment.
• Monitor your data
In order to identify any attempt of security breach, you should have a system in place to monitor the inflow and outflow of your sensitive data to and from your network. One good idea would be to implement data loss prevention and file auditing.
• Protect your website
It is also important to make sure that your business website is protected against any possible Malware attack. To this end, you should take some important steps, such as, setting the secure flag for all session cookies, using SSL, and scanning your site on a regular basis.
• Use network-based security hardware and software
Make sure that you use only Reliable hardware and software, such as, firewalls, honey pots, gateway antivirus, and intrusion detection devices. Remember that installing antivirus software may not be enough to guard your devices against security threats. You need to make sure that you use personal firewall other devices for enhanced security. It is better if you can source your hardware items from your network support in London.
Finally, it is always a good idea to opt for professional help for Network Security in London. Depending on your needs, you can hire an IT consultant in London either for full time or on as-needed basis. Just make sure that you select a vendor that has years of experience and good reputation.